For cybersecurity companies, new trends signal new challenges and opportunities to develop new and strengthen existing systems to continue safeguarding data, support clients, and realize sustained growth.
The cybersecurity landscape is shifting faster than ever. AI is reshaping offense and defense. Privacy laws are tightening.
Ransomware groups are evolving like full-blown corporations. Billions of IoT devices are connecting, many with security as an afterthought. And the rising momentum toward quantum technology is pressuring organizations to rethink cryptography from the ground up.
2026 won’t be about doing more security — it will be about doing smarter, adaptive, data-driven security that protects people, systems, and reputation in a hyper-connected world.
Below are the top 9 cybersecurity trends that will shape security strategies, operations, and policy in 2026
1. Data privacy laws and regulations will get tighter and more complex
As companies employ more AI tools and leverage massive datasets, regulators are responding by pushing stricter rules, especially around cross-border data flows and AI training data. Companies that don’t adapt risk facing multi-million-dollar fines, brand damage, and forced re-engineering of data architecture.
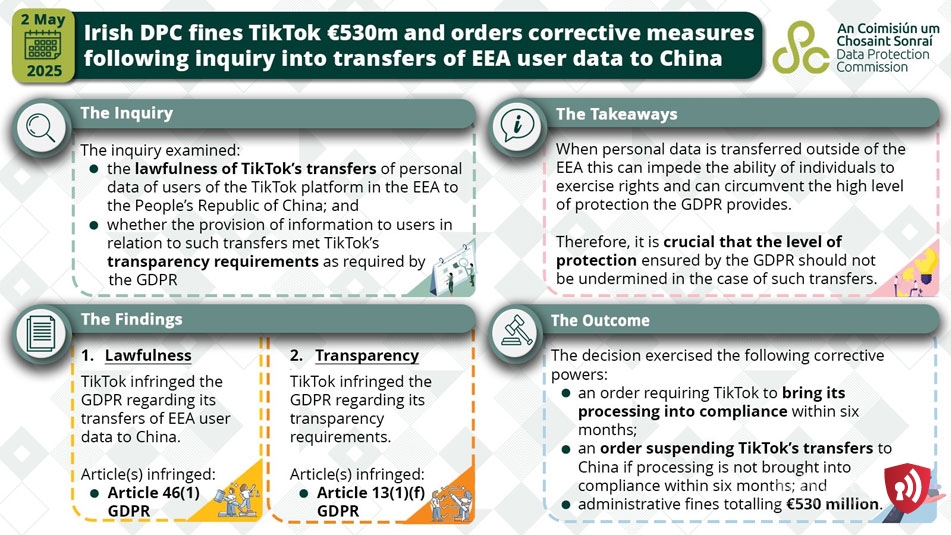
Just recently, TikTok was fined €530 million (~$600 M) by Ireland’s Data Protection Commission for improperly transferring European user data to servers in China.
Compliance is no longer a legal-team checkbox but a core security control. Companies must implement privacy-by-design across data lifecycles, build catalogues that map personal data to systems, and operationalize subject-rights workflows.
Going forward, expect regulators to focus on two technical priorities:
(1). Stronger rules for data used to train or evaluate AI (transparency, provenance, lawful basis)
(2). Stricter requirements for breach notification and cyber incident response plans tied to data breach. Businesses operating across regions will continue to face divergent rules.
For example, U.S. states will keep diverging from EU expectations; hence, investments in automated data governance, consent/notice engines, and regional data localization strategies will rise.
In short, privacy and security teams must collaborate tightly, and privacy compliance will increasingly determine who can deploy large models, share telemetry, or spin up cloud services.
How to stay ahead
To stay ahead of the curve, companies must:
- Build unified data-mapping systems across cloud and on-prem environments.
- Implement privacy-by-design in AI pipelines and applications.
- Automate retention, consent, and deletion workflows.
- Run regional compliance reviews and design for local data handling.
- Hold vendors accountable through privacy SLAs and regular audits.
2. Zero Trust architecture implementation goes mainstream, but maturity lags
In 2023, MGM Resorts, a multinational company that runs popular hotels and casinos in Las Vegas, was breached, causing the company to incur over $100 million in losses. The breach started with a social-engineering attack on a single employee. When attackers gained access, they moved laterally across internal systems. This breach could have been prevented with Zero Trust segmentation.
That’s why Zero Trust Architecture(ZTA) is now mainstream as a strategy, as identity and least-privilege become central to securing distributed IT.
However, surveys and vendor reports show that while 61% of organizations have implemented a defined Zero Trust security initiative, full, measurable maturity remains rare.
That gap matters. Recent research highlights that partial Zero-Trust deployments, for instance, only identity and MFA, without continuous device posture checks, micro-segmentation, and runtime policy enforcement, leave room for compromised devices or untrusted lateral access.
In 2026, defenders will accelerate integration of ZTA across cloud, edge, and SaaS. Identity is now the policy plane for users, machines, and AI agents; continuous conditional access ties telemetry (device health, location, and behavior) to real-time gating; and micro-segmentation limits lateral movement inside hybrid environments.
Implementation will shift from point projects to platform investments and to developer-friendly primitives so teams can bake ZTA into CI/CD pipelines. Expect governance and observability to be the hard parts as organizations must measure policy efficacy, track policy drift, and close remediation loops.
Also, watch regulators and procurement teams. ZTA is increasingly a baseline expectation for critical infrastructure and government contractors.
How to stay ahead
Here’s how to prepare your company for this trend:
- Enforce strong identity controls: MFA, least privilege, and continuous evaluation.
- Add device posture checks to ensure only healthy devices get access.
- Use micro-segmentation to contain breaches.
- Benchmark Zero Trust maturity quarterly.
- Integrate Zero Trust into all new cloud and application projects.
3. AI as a force multiplier for attackers and defenders
AI’s duality is the dominant story of 2026. Attackers use generative AI models to craft highly personalized phishing, automate reconnaissance at scale, generate adaptive malware variants, and run automated “agentic” campaigns that stitch exploits together.
State and criminal actors have already weaponized AI to produce convincing voice and video deepfakes, scale social engineering, and rapidly test exploit chains.
Conversely, cybersecurity experts are deploying AI across detection, triage, threat hunting, and automated response to reduce alert fatigue and prioritize fixes. Studies suggest that 55% of companies now use AI-powered cybersecurity tools as the global AI in cybersecurity market size is projected to $93 billion by 2030.
Evidently, the shift in 2026 is less about whether AI will be used and more about who controls the feedback loops. Adversaries with ready access to stolen corpora and tooling can tune attacks to evade specific organizations’ model-based detectors, while defenders who integrate safe, curated model inputs gain faster, more accurate detection.
Operationally, this means two things:
(1). Security telemetry pipelines must be resilient, provably tamper-resistant, and privacy-compliant so models learn from reliable data
(2). Organizations must implement AI governance (model provenance, explainability, and red-team testing) to prevent defenses from being tricked.
How to stay ahead
Follow these tactics to keep your organization prepared:
- Secure data pipelines feeding security and AI systems.
- Adopt AI governance mechanisms such as model tracking, red-team testing, and bias checks.
- Deploy AI-assisted detection and triage tools.
- Train employees to recognize AI-generated scams.
- Monitor for AI misuse targeting your brand or executives.
4. IoT security threats will continue to increase
Imagine a mass of smart TVs, lights, or other devices forming a botnet, as happened with the BadBox 2.0 botnet, which compromised over 10 million smart TVs and in-car systems, for DDoS campaigns and click-fraud. Or the Mars Hydro data breach, where over 2.7 billion records, including device IDs, Wi-Fi network names, and passwords, were exposed.
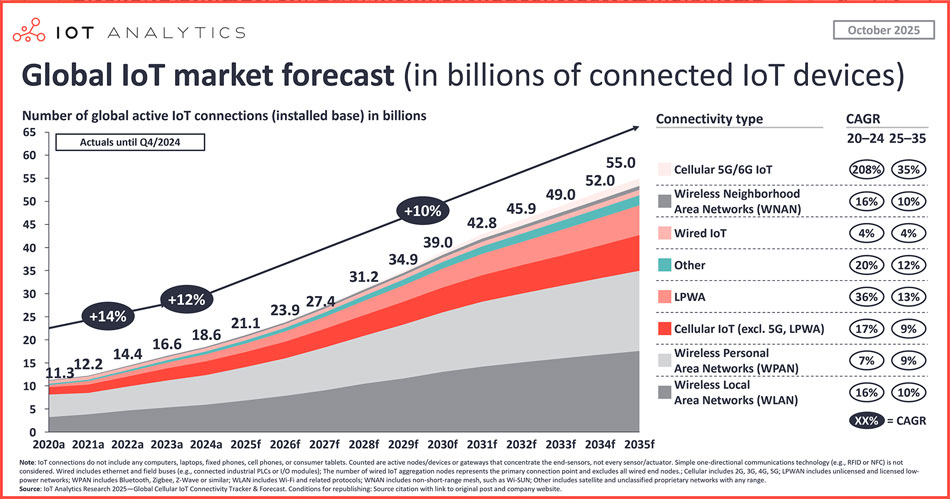
According to statistics, the global IoT market is projected to reach 35 billion connected devices by 2030, but many ship with weak security features, outdated firmware— about 61% lack updates.
That combination invites automated exploitation, device-level botnets, and increasingly cyber-physical attacks, which can disrupt operations, safety-critical systems, or supply chains.
Already, 67% of organizations have experienced at least one IoT-related security incident in the past year.
In 2026, defenders must treat IoT as a first-class security domain by implementing the following:
- Inventory and asset management for non-traditional devices
- Network segmentation that isolates IoT traffic
- Secure boot and hardware root-of-trust adoption
- Automated firmware integrity checks.
Going forward, expect regulators and industry bodies to push baseline standards such as secure defaults, vulnerability disclosure obligations, and minimum update windows while enterprises demand vendor SLAs for security updates.
How to stay ahead
Here are practical strategies to stay safe:
- Maintain a complete IoT asset inventory.
- Segment IoT networks from core systems.
- Require vendors to support patches and secure boot.
- Deploy automated IoT behavior monitoring.
- Retire devices with no update life cycle.
5. Implementation of quantum-ready (post-quantum) security picks up pace
Quantum threat awareness has shifted from theoretical to operational planning. With NIST’s post-quantum cryptography (PQC) standardization milestones and national guidance published, 2026 is the year many organizations move from “planning” to selective deployment of quantum-resistant algorithms.
The key drivers are twofold:
(1). Long-lived secrets such as archival data, legal records, and intellectual property that must remain confidential for decades are vulnerable to “store-now-decrypt-later” attacks.
(2). Governments and critical sectors are accelerating migration roadmaps.
Although practical quantum attacks aren’t here yet, the risk window is opening. Data with long-term sensitivity (medical, financial, government records) must be protected now.
Defenders should take practical steps such as inventorying cryptographic assets, prioritizing high-value keys and protocols for PQC substitution, testing hybrid crypto to reduce risk, and updating TLS stacks, code signing, and VPNs.
We expect cloud providers and major PKI vendors to offer transition toolkits and managed PQC options; meanwhile, guidance from national cybersecurity centers will help frame migration timelines.
Granted, full cryptographic churn is hard since it touches firmware, hardware security modules (HSMs), IoT devices, and embedded systems — so 2026 will be the year of hybrid measures, pilots, and supply-chain coordination, not a clean cutover.
How to stay ahead
Here’s how to stay ready:
- Inventory all cryptographic systems across apps, devices, and networks.
- Prioritize long-term confidential data for PQC protection.
- Test hybrid classical + PQC implementations.
- Work with vendors to ensure hardware and cloud services are PQC-ready.
- Follow NIST PQC standards and roadmap.
6. Increased focus on employee training and cyber awareness programs
Technology alone can’t close the gap as human error remains the top vector for social engineering and credential compromise.
According to a 2025 report, human error accounts for 68% of data breaches. Deepfake scams are also rising. In 2024 alone, Entrust, a multinational company providing identity-centric security tools, reported that organizations experienced deepfake attacks every five minutes.
Case example, finance or HR staff are tricked by a highly realistic deepfake voice or video calls from “executives” requesting wire transfers. These kinds of synthetic attacks are already in use.
In one case, a company lost US$494,000. During the event, the company’s finance director was requested to join a deepfake video call via a Zoom meeting that impersonated their CFO and was deceived into transferring that amount into the scammers’ bank account registered in Hong Kong, China.
What does this imply? With AI-generated phishing and voice/video deepfakes rising, awareness programs that were checkbox-style won’t suffice.
Effective programs will be continuous, contextual, and empathy-driven, blending micro-learning, realistic simulated phishing, role-specific scenarios, and measurable behavior metrics.
Firms deploying sustained programs see steep reductions in susceptibility; organizations are also shifting from punitive cultures to supportive, incident-reporting cultures to speed detection and response.
Another trend to watch out for is security training tied to onboarding and repeated in the first 90 days, because new hires remain disproportionately targeted.
Training will also extend to privileged users, cloud-native developers, and AI model users, focusing on teaching secure prompt design, data handling rules, and how to report suspected model-poisoning.
Finally, expect vendors to ship AI-aided training platforms that personalize simulations and scale to global workforces, reducing the cost of high-quality programs.
How to stay ahead
Here is how to safeguard your organization:
- Use continuous, bite-sized training instead of annual checkboxes.
- Include deepfake awareness, AI-driven phishing, and social-engineering training.
- Train new hires intensively during the first 90 days.
- Encourage a no-penalty reporting culture for suspicious activity.
- Tailor training for roles like finance, HR, developers, and executives.
7. Strengthening the weakest link — supply chain, third parties, and contractors
Supply chain compromise is already a major issue in ransomware. Hackers use a third-party vendor’s MFT application to exfiltrate data, then pressure victims via extortion. Without strong third-party security governance, organizations are exposed to the full risk of their suppliers.
For example, the ransomware group Cl0p exploited zero-day vulnerabilities in Cleo managed file transfer (MFT) software (CVE-2024-50623, CVE-2024-55956), which affected over 60 organizations that use these platforms.
Such a supply-chain breach not only causes financial damage but also undermines trust, forces incident response, and may lead to cascading regulatory consequences.
As attacks through suppliers and managed service providers continue to increase, 2026 brings further scrutiny on vendor cyber hygiene as enterprises realize perimeter controls don’t protect from a trusted partner’s compromise.
Expect risk programs to evolve from not just questionnaires, but continuous monitoring, contractual security SLAs, and stronger segmentation between vendor and core production systems.
Regulators and procurement teams will mandate tighter controls for critical suppliers, such as background audits, minimum patching cadence, and incident notification timelines.
On the technical side, secure software supply-chain practices, including reproducible builds, code signing, dependency SBOM inspections, and runtime integrity checks, will be operationalized in CI/CD.
Heading forward, managed service providers and cloud integrators will face more audits; insurers will press for vendor cyber posture evidence as part of underwriting.
How to stay ahead
Follow these tricks to stay safe:
- Require SBOMs, security SLAs, and breach-notification timelines from vendors.
- Continuously monitor third-party risk — not just annual questionnaires.
- Use code-signing, reproducible builds, and verified dependencies.
- Limit vendor permissions and segment their access.
- Audit MSPs and critical suppliers regularly.
8. Ransomware-as-a-Service(RaaS) and professionalized extortion groups will keep evolving
Ransomware remains a top systemic threat in 2026. Reportedly, in Q1 2025, ransomware attacks increased by 213% compared to Q1 2024.
Several ransomware groups and successor variants that have dominated headlines include:
- Cl0p: In February 2025, the group listed 335 victims in a single month, exploiting zero-days in Cleo’s software (CVE-2024-50623, CVE-2024-55956) to exfiltrate data instead of just encrypting.
- Akira: Reported a large uptick in attacks that averaged 67 attacks per month in early 2025, up from 25 per month in 2024.
- Medusa: Claimed over 40 victims in just January–February 2025, including a U.S. healthcare organization. The ransomware group operates a double-extortion model that includes encrypt and data leak with countdown-based ransom threats.
Reportedly, public-private advisories and takedown operations have disrupted some platforms, but the business model’s incentives persist, spawning new affiliates and variants.
For defenders, the consequences are:
(1). Multi-pronged extortion
(2). Targeted attacks on backups, MSPs, and identity providers
(3). Higher-value demands and double/triple extortion schemes.
Key stakeholders must implement countermeasures that focus on immutable backup architectures, ransomware-resilient restore plans, hardened MSP onboarding, rapid forensic playbooks, and legal/insurance coordination.
Other measures include cyber threat intelligence that maps RaaS pipelines, leak-site behaviors, and negotiation tactics.
How to stay ahead
Here is how to protect your and your clients’ organizations:
- Deploy immutable, offline, and tested backups.
- Patch identity systems and secure remote access.
- Monitor for data exfiltration, not only encryption behavior.
- Run ransomware tabletop exercises with leadership.
- Track RaaS groups via cyber threat intelligence tools.
9. Strengthening cloud and edge security — hybrid controls, posture automation, and data governance
Cloud and edge have become the backbone of modern applications and the locus of escalating attacks. According to a recent report, 61% of organizations have experienced a cloud security incident in the past 12 months.
Without automated posture management and policy-as-code, cloud deployments are vulnerable to drift, which attackers exploit. On the edge, compromised devices may bypass centralized controls as attackers can infiltrate via insecure mesh connections or weak identity enforcement.
In 2026, the priority is continuous cloud posture management, which encompasses automating discovery, misconfiguration detection, and remediation across multi-cloud and edge environments.
Misconfigurations and poorly governed services still drive the majority of cloud incidents, so infrastructure-as-code guardrails, policy as code, and automated drift detection will become table stakes.
Meanwhile, the rise of edge computing introduces latency-sensitive, mission-critical workloads that demand new security patterns such as distributed identity, secure service meshes, runtime attestation for edge nodes, and encrypted telemetry to central analytics.
Moving forward, expect a surge in CSP-offered security services and a marketplace where cloud vendors deliver hardened defaults, managed detection, and integrated posture analytics.
Developers will be expected to “shift left” — embedding security checks in pipelines, using RAG-aware secrets handling, and relying on AI to triage code risk.
For enterprises, the architectural shift is toward zero-trust, policy-driven security fabrics that span cloud, on-premises, and edge, plus tighter collaboration with cloud providers on incident response and lawful data access.
How to stay ahead
Follow these tactics to safeguard your organization:
- Automate cloud posture management and misconfiguration detection.
- Embed security into infrastructure-as-code pipelines.
- Require device attestation and Zero Trust for edge devices.
- Enforce encryption, logging, and centralized monitoring across platforms.
- Review cloud provider shared-responsibility models carefully.
Is Your Organization Prepared?
These cybersecurity developments highlight the importance of developing a proactive, multi-layered strategy to protect against changing attacks as 2026 draws near.
To stay ahead, cybersecurity teams must act with urgency and intention. Start by strengthening identity and access controls, since nearly every major trend, from Zero Trust to cloud and edge security, depends on it. From there, build a living data map so privacy, compliance, and AI governance aren’t guesswork.
Next, invest in continuous training programs that prepare employees for AI-enhanced phishing and synthetic attacks, and establish clear, safe reporting pathways to surface incidents early.
Simultaneously, begin your post-quantum migration roadmap, focusing first on long-lived or high-value data. Then expand visibility across suppliers, MSPs, and cloud workloads through SBOMs, automated posture management, and contractual security requirements.
Finally, assume breach: rehearse ransomware and deepfake-enabled fraud scenarios with legal, PR, and executive teams to ensure resilience under pressure.
Author
 Boniface Kisina is a dedicated cybersecurity content writer with a knack for translating complex security concepts into clear, compelling narratives. With over 4 years of experience in the cybersecurity and tech space, he crafts expert-driven articles that help both technical professionals and everyday readers make sense of cyber threats, trends, and best practices. I have written for a couple of cybersecurity blogs, including Cyber Sierra, Atlas Systems, and more. When he’s not writing, Boniface engages in community work.
Boniface Kisina is a dedicated cybersecurity content writer with a knack for translating complex security concepts into clear, compelling narratives. With over 4 years of experience in the cybersecurity and tech space, he crafts expert-driven articles that help both technical professionals and everyday readers make sense of cyber threats, trends, and best practices. I have written for a couple of cybersecurity blogs, including Cyber Sierra, Atlas Systems, and more. When he’s not writing, Boniface engages in community work.

